The right way to send a secret message to anyone, understanding the basics of 3 pass protocol
The number of ways to trick an AI in an AI proctored exam. These are the most basic limitations of an AI which can never compete with real intelligence of the students.
Everything wrapped up from the latest event CES 2021 from intel and AMD. The rivalry and the greatest laptop processor battle launch after the desktop processor battle.
One of the hardest concept asked in the entrance exams and interview of FAANG(Facebook , Amazon , Apple , Netflix and Google), explained in the easiest way. It also falls in the category of FANG obsessive topics because of its logical recursion replacement.
Major giveaway of a certied penetration testing or hacker training worth Rs.30,000 or $410 on the occasion of our 1 year anniversary. Particiapte now!!
When Linux 1.0 was released to the world more than 30 years ago, it’s model of free and open-source software knocked down all of the walls that had previously been put in place by proprietary software giants like Microsoft to maintain control over the development and distribution of computer programs.
This post is a walkthrough of the PickleRick which is a Rick and Morty themed Tryhackme room. The goal is to find three hidden flags.
The first major step in the software development field is having proper knowledge and understanding of the object-oriented programming concept and its implementation.
These are the most important libraries for anyone who uses python programming languages. Top 6 libraries which are also in daily use of all the top-notch companies.
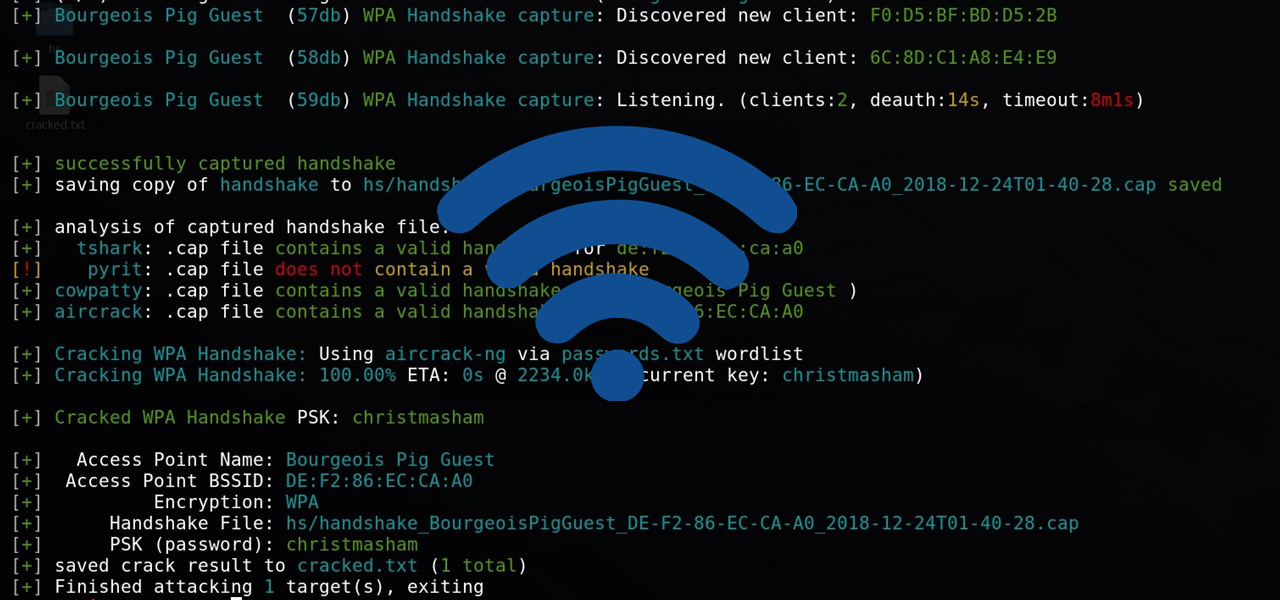
The most basic steps and explanation to crack any WPA, WPA2-PSK networks using Airmon-Ng.